- STMicroelectronics Community
- STM32 MCUs
- STM32 MCUs Embedded software
- how to differentiate boot code data and applicatio...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
how to differentiate boot code data and application data in .HEX file
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Email to a Friend
- Report Inappropriate Content
2023-11-23 12:46 AM
hi I'm using stm32f439 ARM controller for my development here im calculating checksum by accessing my code memory starting from 0x08000000 to up to 2Mb data and EXORING for my code checksum. but when i calculate the data from .HEX its not same, so some source get to know that .HEX file contains boot code data too so how to differentiate boot code data and my code data in .HEX file.
@stm32f439
thank you
suguresh M
- Labels:
-
STM32Cube MCU packages
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Email to a Friend
- Report Inappropriate Content
2023-11-23 6:13 AM
If you XOR the entire memory space does it matter?
You probably want something more robust.
The HEX file is apt to have void and can potentially be non-linear. To check or sign you need to convert to a binary using the same fill or pad values as the writing tool and Flash default.
To recover symbols for different data lengths and structures you could use the .ELF object, or store values in recoverable locations like the vector table.
Up vote any posts that you find helpful, it shows what's working..
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Email to a Friend
- Report Inappropriate Content
2023-11-23 10:50 PM - edited 2023-11-23 10:54 PM
hi Tesla
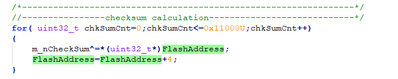
DeLorean actually its for our application requirement I'm doing it. means once i loaded the code means next time it will calculating 32bit checksum for my requirement. Flash address is 0x08000000 where our application starts storing in flash.
Is .BIN file only holds application information or boot data too?
- FreeRTOS app wakes up earlier than RTC requested from standby in STM32 MCUs Embedded software
- STM32WB09 AoA: Unstable/Incorrect IQ Reports with 4-Antenna Switching Setup in STM32 MCUs Wireless
- Bare-Metal OS for STM32F746 with Dynamic ELF Loader in STM32 MCUs Embedded software
- STM32H7B3I-EVAL board (MB1331-H7B3LIQ-D04) RAM and Flash usage estimation in STM32 MCUs TouchGFX and GUI
- OEMiRoT Example on STM32C5: Bugs and CMake / CubeIDE Configuration in STM32 MCUs Embedded software